01 The Day the World Shook
On Saturday morning, February 28, 2026, Tehran was still blanketed in early spring fog. Nobody saw it coming: over the next 12 hours, nearly 900 airstrikes would hammer Iranian territory [1]. This was not some spur-of-the-moment attack. It was the endgame of an intelligence operation years in the making — hacking, AI, spy networks, and raw military firepower all converging on one target.

Israel codenamed the operation Roaring Lion. Washington called it Epic Fury. But regardless of the name, the number one priority target was singular: the Leadership House compound — the residence and office of Supreme Leader Ali Khamenei, located on Pasteur Street in the heart of Tehran [2].
Campaign Outcome
Ali Khamenei — Iran's Supreme Leader, who held absolute power for 37 years — was killed. Iran officially confirmed his death one day later [3].
Along with him, Defense Minister Aziz Nasirzadeh and at least 6 other senior officials were also eliminated. The IDF declared a total of 40 senior commanders killed in the opening wave alone [4].

But what really shook the intelligence world was not the bombs themselves — it was how Israel quietly turned the very surveillance network Tehran built to watch its own people into the enemy's eyes. Thousands of traffic cameras put up to catch red-light runners wound up guiding missiles straight to the compound where the Supreme Leader was working [5].
02 Timeline: From Infiltration to Elimination

Here is the thing that makes this story both brilliant and terrifying: it did not start on February 28, 2026. It started years before that, when the first lines of code slipped into Tehran's camera network and nobody noticed a thing.


03 Hacking Tehran's Traffic Cameras — Technical Details
This is where it gets really interesting — and if you work in cybersecurity, this is where you should start paying close attention.
Iran's Surveillance Camera Network

For years, Iran had built one of the densest surveillance camera networks in the Middle East. Its original purpose? Tracking dissidents, monitoring protests, and checking whether women were wearing the hijab. According to AP, the network spanned across Tehran and other major cities, serving the regime's social control apparatus [5].
The bitter irony: the system built to shield the regime became the enemy's eyes. A Tehran city council member later tacitly confirmed that images from the capital's traffic camera network had indeed been transmitted abroad, and Israel had used them [16].
C2 Channel (Command and Control) and How Data Flowed Back to Israel
According to the Financial Times, video from nearly the entire Tehran traffic camera network was encrypted and regularly transmitted to servers in Tel Aviv for years [6]. Think about it — thousands of cameras streaming video continuously across borders without Iran ever detecting it. This speaks volumes about the attacker's sophistication:
Nation-State C2 Infrastructure — Technical Details
Encrypted tunnel: Data was encrypted end-to-end before transmission, bypassing Iran's Deep Packet Inspection (DPI). Most likely using domain fronting techniques or disguising traffic as legitimate HTTPS.
Bandwidth management: Streaming full video from thousands of cameras would be too "noisy." The system may have used local AI to filter, sending only frames containing valuable information (e.g., when official motorcades were detected) or metadata (license plates, locations, timestamps).
Firmware-level persistence: Maintaining access for years undetected implies firmware-level rootkits — malware that survives even factory resets. Combined with scheduled beaconing (contacting C2 on a schedule, not continuously) to avoid detection through traffic analysis.
Specific CVE Vulnerabilities in Hikvision/Dahua Cameras
Although no official report names exactly which CVEs were used in the Tehran campaign, we can narrow down the likely candidates with considerable accuracy based on publicly disclosed vulnerabilities in the camera models prevalent in Iran — primarily Hikvision and Dahua, both originating from China [17]:
Hikvision — Most Critical CVEs
| CVE | CVSS | Type | Technical Details |
|---|---|---|---|
| CVE-2021-36260 | 9.8 | Command Injection | System command injection via HTTP request, no authentication required. Affects 100M+ devices. Exploited by Mirai botnet and multiple APT groups. CISA listed in KEV "must patch" catalog. 80,000+ cameras still unpatched as of 2022 (per BleepingComputer/Cyfirma). |
| CVE-2017-7921 | 9.8 | Auth Bypass | Direct access to video stream and configuration by injecting parameters into the URL: http://[ip]/onvif-http/snapshot?auth=YWRtaW46MTEQA forged base64 string is enough to completely bypass authentication. Added to CISA KEV catalog. Discovered in 2017, still present on millions of devices. |
| CVE-2025-34067 | 10.0 | RCE (Remote Code Execution) | RCE on Hikvision iSecure Center (centralized camera management platform, Chinese market) via endpoint /bic/ssoService/v1/applyCT. Fastjson deserialization → loads arbitrary Java class via LDAP URL. PoC exploit publicly available. Shadowserver detected exploitation since 02/2025. Note: HikCentral (international version) is not affected according to Hikvision. |
| CVE-2013-4977 | 10.0 | Buffer Overflow | Buffer overflow in RTSP handler (Range parameter) → arbitrary remote code execution, no authentication required. Affects Hikvision DS-2CD7153-E and similar models. Cameras also contain hidden accounts (anonymous) with hardcoded credentials. |
Dahua — ONVIF and RCE Vulnerabilities
| CVE | CVSS | Type | Technical Details |
|---|---|---|---|
| CVE-2021-33044 | 9.8 | Auth Bypass | RPC2 login accepts empty-password hash → complete authentication bypass → admin takeover. PoC publicly available since 10/2021. Affects IPC-HX3XXX, HX5XXX, VTO, PTZ, Thermal. Listed in CISA KEV catalog. |
| CVE-2022-30563 | 7.4 | Replay Attack | Man-in-the-middle sniffing of unencrypted ONVIF communications (WS-UsernameToken) → replay credentials in new requests → create admin account and fully compromise camera. |
| CVE-2025-31700 CVE-2025-31701 |
8.1 | Buffer Overflow | Stack overflow in ONVIF request handler (Host header) and .bss overflow in RPC upload handler. Crafted packet → RCE or DoS, no authentication required. Affects IPC-1XXX, IPC-2XXX, SD series. Patched since 16/04/2025. |
Common Characteristics - "Open Doors"
Both Hikvision and Dahua share systemic weaknesses that make infiltration frighteningly easy:
1. RTSP streams are typically unencrypted (plain text) - anyone who intercepts traffic can watch the video.
2. HTTP/HTTPS admin interfaces exposed directly on the internet - a Shodan scan finds them.
3. Unchanged default credentials (admin/admin, admin/12345).
4. Firmware rarely updated in Iran (due to sanctions, lack of manufacturer technical support).
5. Camera network not segmented (flat network) - compromising 1 camera = access to entire network.
6. No firmware integrity checking mechanism - firmware-level rootkits never detected.
According to TechCrunch, "urban camera networks are notoriously soft targets — many cameras stream unencrypted video or use default passwords, and data often runs through unsegmented city IT infrastructure" [17]. In other words, Unit 8200 did not need to be geniuses — Iran had already left the door wide open.
Infiltrating Iran's Mobile Network — SS7/Diameter
Alongside the camera hack, Israel also "deeply penetrated Iran's mobile phone network" [6]. This was the second front, and technically may have been even more complex.
Mobile Network Infiltration Techniques — Analysis
SS7 exploitation: The SS7 protocol (Signalling System 7) — the backbone of 2G/3G networks — contains design-level vulnerabilities that allow anyone with access to the signalling network to send location tracking commands, intercept SMS, and redirect calls. MTN Irancell — Iran's largest carrier — maintains SS7 roaming connections with Gulf carriers near U.S. military bases [18].
Diameter protocol (4G/LTE): The "more modern" successor to SS7, but still containing similar vulnerabilities. Allows querying device locations, intercepting data, and spoofing network identities from anywhere in the world with access to the signalling network.
IMSI Catcher: A device that simulates a cell tower (fake cell tower). Khamenei's security detail's phones automatically connect → IMSI (subscriber identity), call metadata, messages, and precise location are captured. Israel has world-leading IMSI catcher technology — many companies founded by Unit 8200 veterans manufacture these devices.
SIM cloning / Intercept: With SS7 access, any phone number's location can be tracked without physical proximity. Combined with traffic cameras → cross-referencing mobile location + vehicle images = precisely identifying who is where, and when.
Disabling Mobile Antennas — The "Busy Signal" That Sealed His Fate
This is the most chilling detail. Just before the strike, Israel tampered with approximately 12 mobile antennas near Pasteur Street — where Khamenei's compound was located. The result: anyone calling the phones of Khamenei's security detail received a busy signal. As missiles were inbound, no one could warn the protection team [22].
Techniques for Localized Mobile Network Disruption
Fake eNodeB (SDR-based): Using Software Defined Radio (SDR) equipment to create a fake 4G cell tower. Phones in the area automatically connect to the fake tower (stronger signal) → attacker gains full control — blocking calls, SMS, keeping phones perpetually "busy."
SS7 call redirection: Instead of physically jamming signals, SS7 commands redirect calls to the security detail's numbers to voicemail or non-existent numbers — callers hear "busy" without suspecting anything.
Selective jamming: Targeted signal jamming — only creating interference within a narrow radius around the compound, without affecting the entire city (to avoid early detection).
Tactical significance: 12 tampered antennas = the security detail was "blind and deaf" at the decisive moment. When someone spotted the missiles and tried to call a warning → busy signal → Khamenei was not evacuated in time to safety.
Supporting Cyber Warfare — TV Hijacking
Beyond cameras and mobile networks, the cyber campaign included another audacious move: after airstrikes destroyed the headquarters of two state TV networks (IRIB), Israel hijacked the broadcast and aired speeches by Trump and Netanyahu calling on the Iranian people to rise against the regime [17]. According to TechCrunch, U.S. military officials confirmed that "coordinated cyberspace operations effectively disrupted communications systems and sensor networks" in Iran prior to the attack [17].
Precision Weapon — The Blue Sparrow Missile
The entire intelligence chain above reportedly served one final strike: the Blue Sparrow missile — an air-launched weapon that may have been employed from F-15s, developed by Rafael Advanced Defense Systems. According to Army Recognition, Israel "May Have Employed" Blue Sparrow missiles in the early waves of the campaign [23].
Blue Sparrow — "From Outer Space"
Specifications: Length 6.51m, weight 1.9 tons, range ~2,000 km, single-stage solid fuel propulsion.
Quasi-ballistic trajectory: After launch, the missile ascends beyond the atmosphere (suborbital) then re-enters at a near-vertical angle at extreme velocity. This "falling from the sky" trajectory makes Iran's missile defense systems (S-300, Bavar-373) nearly incapable of interception.
Guidance: INS (inertial navigation system) combined with GPS/GNSS satellite → meter-level accuracy. The 14-digit coordinates from the AI system were loaded directly into the guidance system.
Why Blue Sparrow: Originally designed to test the Arrow missile defense system, reportedly converted into an offensive weapon. Launched from aircraft outside Iranian airspace → missile flies in autonomously → extremely difficult to intercept.
Looking back at all 5 layers, this was a campaign that converged at least 5 specialized domains: exploit IoT/CCTV → encrypted video exfiltration → AI computer vision + graph analysis → cellular manipulation → precision strike. No single vulnerability determined the outcome — it was the entire technical chain operating seamlessly over multiple years. And Iran, despite having been warned multiple times by its own lawmakers [16], failed to respond in time.
04 The "Target Production Machine" — AI in Warfare

If the camera hack concerns you, this part should deeply concern you. Israel did not stop at collecting data. They built an entire AI ecosystem to automate the full pipeline: from raw data to kill coordinates.
"An AI-powered target production machine, capable of processing massive amounts of data. Inputs include imagery intelligence, human intelligence, signals intelligence, intercepted communications, satellite images. The output is a precise location — in the form of a 14-digit grid coordinate."
— Israeli intelligence source, Financial Times [6]Inside Gospel and Lavender — How the AI "Thinks"
Information from +972 Magazine and military sources reveals that these two AI systems operate in far more specific ways than most people realize [19]:
Lavender — "The Kill List Factory"
Inputs (features): Video feeds, intercepted messages, social media data, phone communications, SIM change history, address change history, WhatsApp group memberships, social connections, photos.
Scoring mechanism: Each individual is assigned a "suspicion" score based on a combination of features. For example: membership in a WhatsApp group containing known combatants → +points. Changing SIMs every few months → +points. Frequently changing addresses → +points.
Accuracy: According to +972 Magazine, based on Israeli military sources in the Gaza campaign, the system achieved a 90% accuracy rate — meaning 10% were false positives (flagging individuals with loose or no actual connections). The Israeli military accepted this rate and authorized widespread use.
Speed: Before Lavender, human analysts produced approximately 50 targets/year. Lavender + Gospel produces 100 targets/day — roughly 730 times faster.
Gospel (Habsora) — "Infrastructure Target Map"
Function: Automatically scans reconnaissance data (drone, satellite, SIGINT) to identify buildings, equipment, and vehicles belonging to the adversary.
Deep learning: Uses image recognition neural networks to classify targets from satellite/drone imagery — distinguishing between military barracks, weapons depots, command centers, and civilian facilities.
Process: Gospel proposes a target → human analyst reviews (typically taking about 20 seconds per target, according to +972 Magazine) → approval → coordinates sent to strike unit.
Social Network Analysis — Peeling Back Every Layer of Protection
Perhaps the most sophisticated technique in the entire campaign was how Unit 8200 employed mathematical social network analysis on billions of data points [8]. Not "social media" in the Facebook sense — but algorithms analyzing relationships among millions of people based on communications, movement, and behavioral data.
How Social Network Analysis Broke Khamenei's Security Apparatus
Step 1 — Identify "nodes": Every bodyguard, driver, and aide around Khamenei was a node in the social graph.
Step 2 — What traffic cameras revealed: Tracking bodyguards' personal vehicles → knowing where they lived, which shifts they worked, where they parked near the compound. According to the Financial Times, one camera had a vantage point overlooking the spot where bodyguards parked — and that was the decisive clue.
Step 3 — Mobile data supplements: Who called whom, at what time, from which cell tower. Combined into a complete relationship map.
Step 4 — AI identifies "center of gravity": The algorithm found seemingly ordinary individuals who were actually critical links — people whose removal would throw the entire protection network into disarray.
Step 5 — Complete "Pattern of Life": Routes, schedules, personnel, habits. As one Israeli source described it: "We knew Tehran like we knew Jerusalem" [10].
05 Kill Chain Analysis
Viewing the entire campaign through the lens of the Lockheed Martin Cyber Kill Chain, extended for hybrid warfare:
06 MITRE ATT&CK Mapping
Below are the attack techniques used (or very likely used), mapped to the MITRE ATT&CK framework — the global cybersecurity industry standard for classifying attack techniques:
| ID | Technique | Application in This Campaign |
|---|---|---|
| T1190 | Exploit Public-Facing App | Exploiting internet-exposed IP camera vulnerabilities (RTSP, ONVIF, HTTP admin panel) |
| T1195 | Supply Chain Compromise | Planting backdoors in camera firmware/hardware before installation in Iran |
| T1078 | Valid Accounts | Using default passwords (admin/admin) that Iran never changed |
| T1021 | Remote Services | Lateral movement from cameras to control center via SSH/RDP |
| T1132 | Data Encoding | Encrypting video streams before exfiltrating to Tel Aviv |
| T1029 | Scheduled Transfer | Transmitting data on schedule (scheduled beaconing) to avoid detection |
| T1542 | Pre-OS Boot (Firmware) | Firmware rootkit maintaining access through factory resets |
| T1125 | Video Capture | Continuous video capture from Tehran's traffic camera system |
| T1040 | Network Sniffing | Sniffing internal traffic from compromised cameras to discover additional targets |
07 Unit 8200 & Mossad — The "Architects" of the Campaign
Discussing Israeli cyber intelligence without mentioning Unit 8200 is like discussing Silicon Valley without mentioning Google. This is the most elite SIGINT (signals intelligence) unit in the Israeli military, the equivalent of America's NSA — but with a startup mentality: lean, audaciously creative, and willing to break the rules. Many Unit 8200 veterans have gone on to found prominent cybersecurity companies: NSO Group, Check Point, Wiz, CyberArk... [10]
Unit 8200 — SIGINT
- Signal collection (cameras, mobile, satellite)
- AI development & operation (Gospel, Lavender)
- Penetrating Iran's network systems
- Social Network Analysis on billions of data points
- Producing target coordinates for the air force
Mossad — HUMINT
- Recruiting human sources inside Iran
- Cross-verifying SIGINT information
- "Last mile" intelligence — what cameras cannot see
- Coordinating with CIA to confirm Khamenei's location
The combination of SIGINT + HUMINT + IMINT + AI created what analysts call Multi-INT Fusion — the convergence of multiple intelligence sources. This represents the current pinnacle of military intelligence tradecraft, and the 28/02 campaign was the first real-world test at the national scale.
08 From Stuxnet to Roaring Lion — 16 Years of Evolution
Stuxnet (2010) — The First Cyber Weapon to Destroy Physical Infrastructure
Stuxnet is a name that anyone studying cybersecurity must know. Discovered in 2010, it was the first cyber weapon in history to cause physical damage to industrial infrastructure — ushering in a new era of warfare where code could destroy real machines.
The target: Iran's Natanz uranium enrichment facility, where thousands of IR-1 centrifuges spun at supersonic speeds to separate the U-235 isotope. Stuxnet is believed to be a joint effort between the U.S. (NSA) and Israel (Unit 8200) under a classified program codenamed Operation Olympic Games.
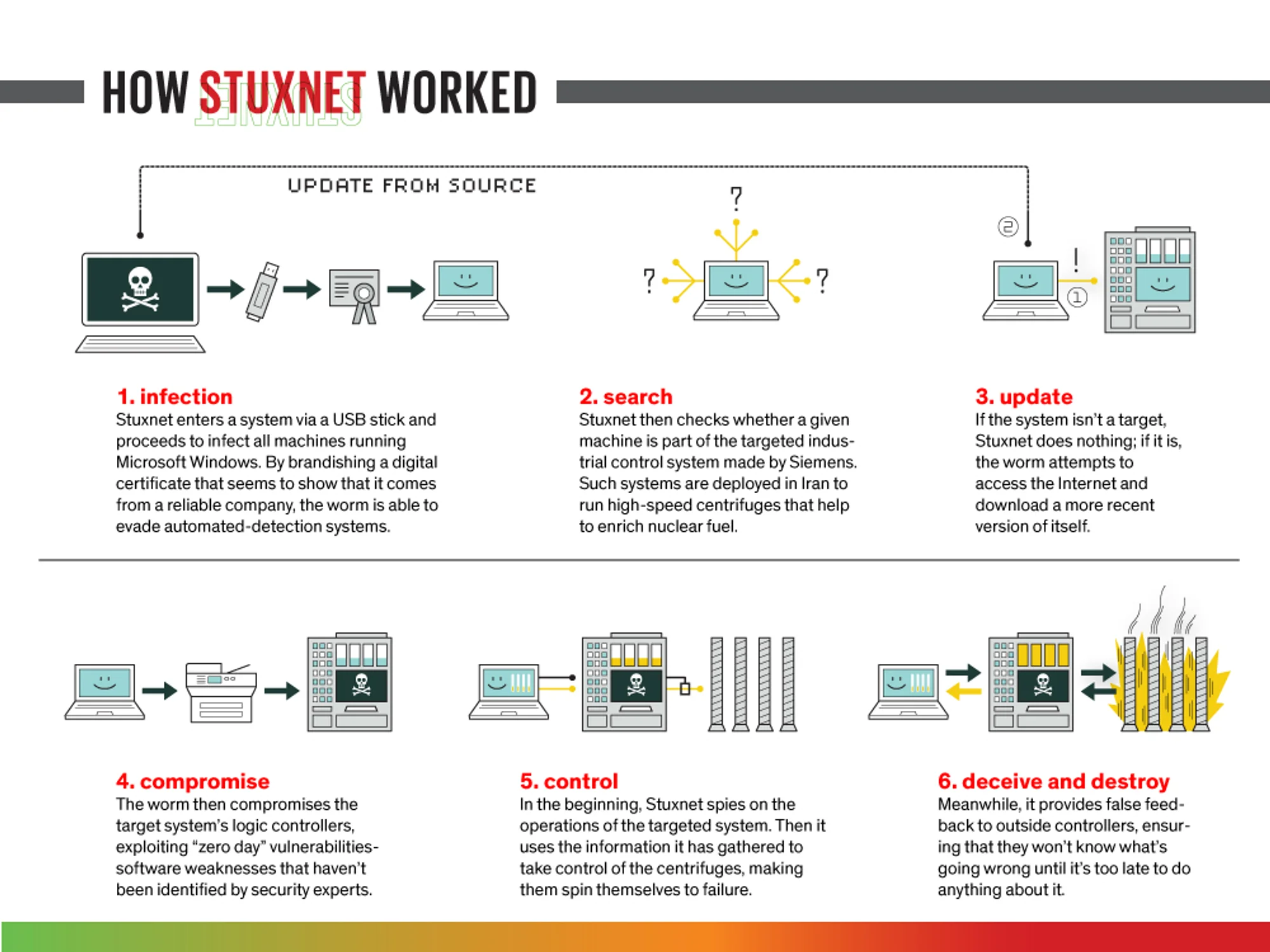
How Stuxnet Worked — 6 Stages
1. Infection: Stuxnet infiltrated via USB drives — because Natanz was an air-gapped network (no internet connection). The worm self-replicated through every USB plugged into Windows computers, exploiting 4 zero-day vulnerabilities previously unknown — an unprecedented number.
2. Search: After infecting a Windows machine, Stuxnet did not activate immediately. It silently checked: is this computer connected to a Siemens Step 7 SCADA system? If not → lie dormant and continue spreading. If yes → proceed to the next stage.
3. Update: Upon finding a Siemens SCADA system controlling the frequency converters of centrifuges, Stuxnet connected to the internet (if available) to download the latest version of itself.
4. Compromise: Stuxnet exploited zero-day vulnerabilities in Siemens Step 7 software to seize control of the PLCs (Programmable Logic Controllers) — the brains controlling centrifuge rotation speed.
5. Sabotage: Stuxnet altered centrifuge rotation speeds — pushing them up to 1,410 Hz (vs. the normal 1,064 Hz) then dropping to 2 Hz, creating vibrations that destroyed the fragile aluminum rotors. This process occurred gradually, over many months, causing centrifuges to fail as if from "natural aging."
6. Deceive: This was the most ingenious part — while sabotaging, Stuxnet sent fake data to monitoring screens, displaying everything as normal. Iranian engineers saw OK readings on their screens while the centrifuges were self-destructing. By the time they discovered it, approximately 1,000 centrifuges (nearly 1/5 of the total) had been destroyed.
Historical Significance of Stuxnet
Legal precedent: Stuxnet proved that a cyberattack could achieve strategic objectives (delaying Iran's nuclear program by an estimated 2-3 years) without bloodshed — but also opened "Pandora's box" for every other nation.
Technical breakthrough: Simultaneously exploiting 4 zero-days, stolen digital certificates from Realtek and JMicron, and the ability to attack PLCs — a level of complexity only achievable with nation-state resources.
Unintended consequences: Stuxnet escaped Natanz and spread across the internet, infecting over 100,000 computers in 115 countries. The source code was reverse-engineered and became a "textbook" for other attack groups — including Iran, which subsequently developed its own offensive cyber capabilities (Shamoon, APT33, APT34).
The "Father" of Roaring Lion: Without Stuxnet, there would be no Predatory Sparrow, no Tehran camera hack campaign. Stuxnet proved the principle — cyber can cause physical damage. 16 years later, Roaring Lion took that principle to an entirely new level: cyber is not just destructive, but serves as the intelligence foundation for an entire conventional military campaign.
To understand where the 2026 campaign fits in this evolutionary arc, consider this comparison:
| Criteria | Stuxnet (2010) | Predatory Sparrow (2021-23) | Roaring Lion (2026) |
|---|---|---|---|
| Target | Natanz centrifuges | Civilian infrastructure (railways, gas stations, steel plant) | Supreme Leader + entire military infrastructure |
| Scope | 1 facility | Multiple distributed targets | Nationwide — 900 airstrikes |
| Cyber role | Primary weapon (physical destruction) | Primary weapon (disruption) | Intelligence platform for kinetic strikes |
| AI | None | Limited | Central — automated target production |
| Attribution | Denied | Hacktivist group (suspected Israel) | Publicly claimed |
The Major Turning Point
Stuxnet (2010) proved cyber could cause physical damage. Predatory Sparrow (2021-23) proved cyber could disrupt an entire nation's infrastructure [7]. Roaring Lion (2026) proved cyber + AI can serve as the intelligence foundation for an entire conventional military campaign — a new era [9].
09 Iran Response — The Cyber Front
Iran did not sit idle. Within hours of the airstrikes, more than 60 Iran-linked cyber groups simultaneously mobilized [11]:
Iran's Cyber Counter-Offensive (28/02 – 05/03/2026)
DDoS: Attacks targeting at least 110 organizations across 16 countries, primarily in the Middle East [12].
SCADA/PLC: The FAD Team group claimed to have penetrated Unitronics Vision Series systems in Israel.
Military: 500+ ballistic missiles + 2,000 drones — 40% targeting Israel, 60% targeting U.S. bases [1].
AI-assisted: Hacktivist groups used AI scanning to discover over 40,000 internet-exposed ICS systems [11].
10 Warning for Vietnam: Tehran Is Not Far Away
At this point you might be thinking: "That is Iran's problem — what does it have to do with us?" The short answer: everything. And the reason is quite literally hanging above our heads.

According to Vietnam's Ministry of Information and Communications (now the Ministry of Science and Technology), over 95% of surveillance cameras in Vietnam originate from abroad, primarily Hikvision and Dahua. These devices all have protocols that silently connect back to foreign servers — which itself constitutes a risk of malware and spyware implantation [13].
Even more alarming: approximately 90% of camera systems have never undergone an information security assessment before being put into operation, nor do they receive annual evaluations [14]. In other words, the door is wide open and nobody knows who is watching.
Surveillance Systems Can Become the "Eyes and Ears" of Hostile Powers
The Tehran incident is living proof: a camera system meant to protect national security became a 24/7 non-stop espionage network for the adversary. In Vietnam, this risk is far from hypothetical when most cameras are pushing data to cloud services and servers located abroad.
Every traffic camera, every internet-connected surveillance device is an "eye" that can be hijacked. When hundreds of thousands of cameras nationwide continuously transmit images of streets, intersections, and critical areas to servers outside national territory — that is not merely a cybersecurity risk, but a severe violation of national data sovereignty.
Imagine: if a hostile power gained access to this system — just as Israel did with Tehran — they would be able to track leadership movements, map military deployments, monitor all activities at sensitive locations, and all of this would happen silently, continuously, around the clock. Iran lost its Supreme Leader for precisely this reason.
6 WARNINGS FOR VIETNAM FROM THE TEHRAN INCIDENT
1. Lessons on vendor dependency: Hikvision and Dahua have been restricted from government use by the U.S., UK, and Australia due to security concerns. Critical vulnerabilities in cameras from both manufacturers have been listed by CISA (US) as mandatory emergency patches [15]. Vietnam must ask itself: why are other countries restricting while we are expanding?
2. Known but unpatched vulnerabilities: The Hikvision vulnerability with a CVSS score of 9.8/10 (maximum severity) was discovered in 2021, affecting over 100 million devices. Yet according to The Register, 80,000+ cameras remained unpatched as of 2022 (per BleepingComputer/Cyfirma). Vietnam ranks in the top 5 affected countries [15].
3. Expansion = multiplied risk: The nationwide camera expansion plan through 2050 will increase the attack surface exponentially. Every new camera is another entry point for intruders [13].
4. QCVN 135:2024 must be strictly enforced: Vietnam's national technical standard for surveillance camera security already exists — now it needs enforcement, not just a signed document gathering dust [14].
5. Network segmentation is mandatory: Camera networks MUST be fully segmented from other critical systems. A flat network is an "open invitation" to disaster — Tehran just proved that.
6. Data sovereignty — non-negotiable: Video data from surveillance cameras must be stored and processed on Vietnamese territory, never transmitted to foreign cloud services or servers. Every data stream leaving the border is a potential threat. Data localization must be mandatory for all surveillance camera systems — especially cameras at government, military, and critical infrastructure sites.
Recommendation: Vietnam Must Own Camera Design and Data Infrastructure
The Tehran incident poses an existential question: should national security be entrusted to equipment whose hardware and firmware you cannot control? The answer is clearly no.
Own the camera design: Vietnam needs to invest in developing and deploying surveillance cameras designed by Vietnamese enterprises — from hardware and firmware to management software. With domestic design, the entire chain is controlled: no hidden backdoors, no covert protocols connecting to foreign servers, no dependency on foreign vendors for vulnerability patches. Vietnamese technology companies are fully capable of this — the issue is policy and determination.
Domestic cloud — absolutely: All surveillance video data must be stored and processed on domestic cloud infrastructure, operated by Vietnamese companies, hosted in data centers on Vietnamese soil. Not a single frame from security cameras should leave the nation's digital borders. This is not a recommendation — it must be a mandatory regulation.
Lessons from Tehran: Iran also once believed its cameras were secure. They too believed their surveillance network served national security. The result? The entire system became a weapon in the adversary's hands, operating silently for years without anyone knowing. Vietnam has an advantage Iran did not: we have been forewarned. The question is whether we will act in time.
Physical Attack Risk: Memory Cards — The "Fatal Weakness" Few Consider
Beyond network-based attacks, there is another dangerous vector that most people overlook: physical attacks on camera hardware.
Many modern AI cameras run firmware or even their entire operating system from internal SD/microSD cards. This common design allows easy updates and local video storage — but it is also a fatal weakness.
Attack scenario: An attacker simply climbs the camera pole at night — when foot traffic is minimal and lighting is limited — opens the camera housing, removes the manufacturer's original memory card, and replaces it with a card pre-loaded with malicious firmware. The camera reboots, loads firmware from the new card, and from that point becomes a perfect espionage device — streaming video to the attacker's server, acting as a backdoor into the internal network, or even spreading malware to other devices on the same network.
Why this threat is very real in Vietnam:
• Most outdoor cameras are mounted on light poles and traffic signal poles — with no physical protection preventing tampering.
• Camera housings typically use standard screws, with no tamper-proof seals or lid-opening detection sensors.
• Cameras lack Secure Boot mechanisms — meaning they do not verify firmware integrity before booting. Any memory card inserted is accepted.
• There is no centralized monitoring system to detect when a camera is disconnected or its firmware is abnormally changed.
Recommendation: Physical Protection for Outdoor Cameras
1. Mandatory Secure Boot: All surveillance cameras must support Secure Boot — accepting only firmware that is digitally signed by the manufacturer. If a memory card is replaced with unsigned firmware, the camera must refuse to boot and send an alert to the central system.
2. Tamper detection — Alert when housing is opened: Outdoor cameras must be equipped with tamper switches. When the housing is opened, the camera immediately sends a real-time alert to the central monitoring system — including a photo, GPS location, and exact timestamp. This feature already exists on many premium camera models but is rarely required in deployment projects in Vietnam.
3. Periodic firmware integrity checking: The central management system must automatically verify each camera's firmware hash on a schedule — if the hash changes from the original without going through the official update process, it is a sign of compromise.
4. Tamper-proof housings: Use specialized security screws, QR-verified tamper-proof seals, and vandal-proof housing designs meeting IK10 standards. Opening the housing must leave permanent, non-erasable physical evidence.
11 Cybersecurity Lessons
Strip away the geopolitics and what you are left with is a set of hard lessons that apply to any country or organization:

1. Surveillance Systems Are the "Achilles' Heel"
Iran built a camera network to keep tabs on its people — then left the whole thing wide open. Any IoT or SCADA system plugged into the network without proper security is a double-edged sword. More cameras, bigger attack surface.
2. Supply Chain Is the Most Dangerous Vector
When you rely on foreign equipment — whether because of sanctions or because it is cheap — you are betting national security on the vendor's goodwill. Hardware you cannot trace back to its source is a ticking time bomb.
3. AI Changes the Rules of Intelligence
When AI can process petabytes of data and output 100 targets/day [9], the attacker's decision-making speed far exceeds the defender's ability to respond. This is an arms race where the side without AI will lose.
4. Network Segmentation: Non-Negotiable
If Tehran's camera network had been properly walled off from sensitive systems, the story might have ended differently. Flat network = one way in = everything falls.
5. Continuous Monitoring, Not Periodic Audits
Israel sat inside the network for years and Iran never caught on. Running a vulnerability scan once a quarter does not cut it — you need continuous monitoring, behavioral analytics, and firmware integrity checks running around the clock.
Conclusion
The Roaring Lion / Epic Fury campaign marks a new era: cyber is no longer just a weapon, but the intelligence foundation for an entire conventional military campaign. The combination of SIGINT + HUMINT + AI + kinetic weapons is the template for all future conflicts — and a stark warning for any nation that still takes critical infrastructure cybersecurity lightly. Including Vietnam.
References
- Al Jazeera, "US, Israel attack Iran updates: Khamenei, top security officials killed," Al Jazeera, 28/02/2026. [Online]. Available: https://www.aljazeera.com/news/liveblog/2026/2/28/
- CNN, "How the plot to kill Iran's Ayatollah Ali Khamenei came together using hacked traffic cameras in Tehran and US intelligence," CNN, 03/03/2026. [Online]. Available: https://www.cnn.com/2026/03/03/middleeast/
- NPR, "Iran's supreme leader, Ayatollah Ali Khamenei, has been killed," NPR, 28/02/2026. [Online]. Available: https://www.npr.org/2026/02/28/
- NBC News, "Iran Supreme Leader Ali Khamenei is dead after U.S., Israel attack," NBC News, 28/02/2026. [Online]. Available: https://www.nbcnews.com/world/iran/
- PBS/AP, "Iran built a vast camera network to control dissent. Israel used it to track targets," PBS News, 2026. [Online]. Available: https://www.pbs.org/newshour/
- Financial Times / J. Post, "Israel hacked Tehran's traffic cameras, used AI to plan Khamenei's assassination," Jerusalem Post, 2026. [Online]. Available: https://www.jpost.com/middle-east/iran-news/
- Binding Hook, "Predatory Sparrow: cyber sabotage with a conscience?," Binding Hook. [Online]. Available: https://bindinghook.com/predatory-sparrow/
- Times of Israel, "Report: Israel hacked Tehran traffic cameras to track Khamenei ahead of assassination," Times of Israel, 2026. [Online]. Available: https://www.timesofisrael.com/report/
- Bloomsbury Intelligence and Security Institute, "Iran conflict as a testing ground for AI warfare systems," BISI, 03/2026. [Online]. Available: https://bisi.org.uk/reports/
- Hvylya, "'We Knew Tehran Like Jerusalem': How Unit 8200 Built a Real-Time Map of Iran's Capital," Hvylya, 2026. [Online]. Available: https://en.hvylya.net/news/875/
- Palo Alto Networks Unit 42, "Threat Brief: March 2026 Escalation of Cyber Risk Related to Iran," Unit 42, 03/2026. [Online]. Available: https://unit42.paloaltonetworks.com/
- ZENDATA Cybersecurity, "Cyber Warfare in the US-Israel vs Iran Conflict (Roaring Lion & Epic Fury)," ZENDATA, 02/03/2026. [Online]. Available: https://zendata.security/2026/03/02/
- VietnamNet, "Giảm thiểu thiết bị camera giám sát tiềm ẩn nguy cơ mất an toàn dữ liệu," VietnamNet, 2025. [Online]. Available: https://vietnamnet.vn/giam-thieu-thiet-bi-camera/
- VietnamNet, "Xây dựng quy chuẩn về an ninh hệ thống camera giám sát trong cơ quan nhà nước," VietnamNet, 2025. [Online]. Available: https://vietnamnet.vn/xay-dung-quy-chuan/
- IPVM, "Hikvision Has 'Highest Level of Critical Vulnerability,' Impacting 100+ Million Devices," IPVM. [Online]. Available: https://ipvm.com/reports/hikvision-36260
- Iran International, "Tehran city official confirms traffic-camera images were sent abroad," Iran International, 11/2025. [Online]. Available: https://www.iranintl.com/en/202511178627
- TechCrunch, "Hacked traffic cams and hijacked TVs: How cyber operations supported the war against Iran," TechCrunch, 03/03/2026. [Online]. Available: https://techcrunch.com/2026/03/03/
- National Security News, "The targeting chain: how the IRGC exploits MTN-Irancell's Gulf telecom connections," National Security News, 03/2026. [Online]. Available: https://nationalsecuritynews.com/2026/03/
- +972 Magazine, "'Lavender': The AI machine directing Israel's bombing spree in Gaza," +972 Magazine, 04/2024. [Online]. Available: https://www.972mag.com/lavender-ai-israeli-army-gaza/
- The Hacker News, "Critical Dahua Camera Flaws Enable Remote Hijack via ONVIF and File Upload Exploits," The Hacker News, 07/2025. [Online]. Available: https://thehackernews.com/2025/07/
- Cybernews, "Israel hacked Iran's traffic cameras to pinpoint Khamenei," Cybernews, 03/2026. [Online]. Available: https://cybernews.com/editorial/
- Ynet News, "'We knew Tehran like Jerusalem': inside the operation that eliminated Khamenei," Ynet, 03/2026. [Online]. Available: https://www.ynetnews.com/article/hjayhkqk11e
- Army Recognition, "Israel May Have Employed Blue Sparrow Air-Launched Missiles in Early Waves of Iran Strike Campaign," Army Recognition, 03/2026. [Online]. Available: https://www.armyrecognition.com/news/